A vulnerability in the way that Visa cards work with Apple Pay Express Transit mode “could enable hackers to bypass an iPhone’s Apple Pay lock screen and perform contactless payments”, researchers at the University of Birmingham and the University of Surrey have found.
“The weakness lies in the Apple Pay and Visa systems working together and does not affect other combinations, such as Mastercard in iPhones or Visa on Samsung Pay,” the researchers explain in a paper to be published at the 2022 IEEE Symposium on Security and Privacy.
Visa’s point of view is that it would be impractical for the vulnerability to be exploited in a real-world scenario, however, the payments network has told the BBC.
The researchers discovered the issue after they identified “a unique code broadcast by the transit gates or turnstiles” that support Apple Pay in Express Transit mode which allows users to make contactless fare payments without unlocking their iPhone or authorising the transaction via fingerprint, PIN or Face ID.
“This code […], nicknamed the ‘magic bytes’, will unlock Apple Pay,” the researchers say.
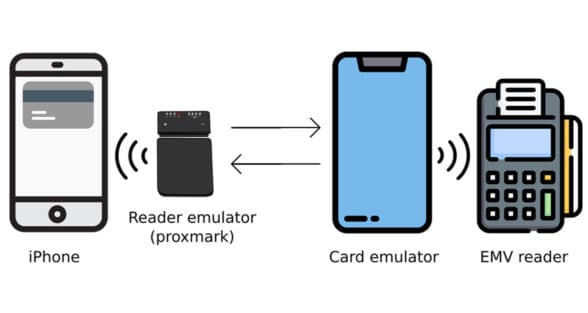
“The team found they were then able to use this code to interfere with the signals between the iPhone and an in-store card reader.
“By broadcasting the magic bytes and changing other fields in the protocol, they were able to fool the iPhone into thinking it was talking to a transit gate, whereas actually, it was talking to a shop reader.
“At the same time, the researchers’ method persuades the shop reader that the iPhone had successfully completed its user authorisation, so payments of any amount can be taken without the iPhone user’s knowledge.”
“This is a concern with a Visa system, but Visa does not believe this kind of fraud is likely to take place in the real world given the multiple layers of security in place,” Apple told the BBC.
“In the unlikely event that an unauthorised payment does occur, Visa has made it clear that their cardholders are protected by Visa’s zero liability policy.”
Next: Visit the NFCW Expo to find new suppliers and solutions